
A massive medical data leak in France reveals a structural flaw in how we secure our most intimate digital identities.

Leaving your Wi-Fi on while walking through the city isn't just a battery drain—it's a massive, overlooked security hole that broadcasts your identity to every malicious actor in range.

Phishing scams targeting tax filings are spiking. Learn how to verify official communications and secure your company's financial data.

Sweden's thwarted attack on a thermal plant reveals a shift in modern warfare where bits freeze pipes before bullets fly.
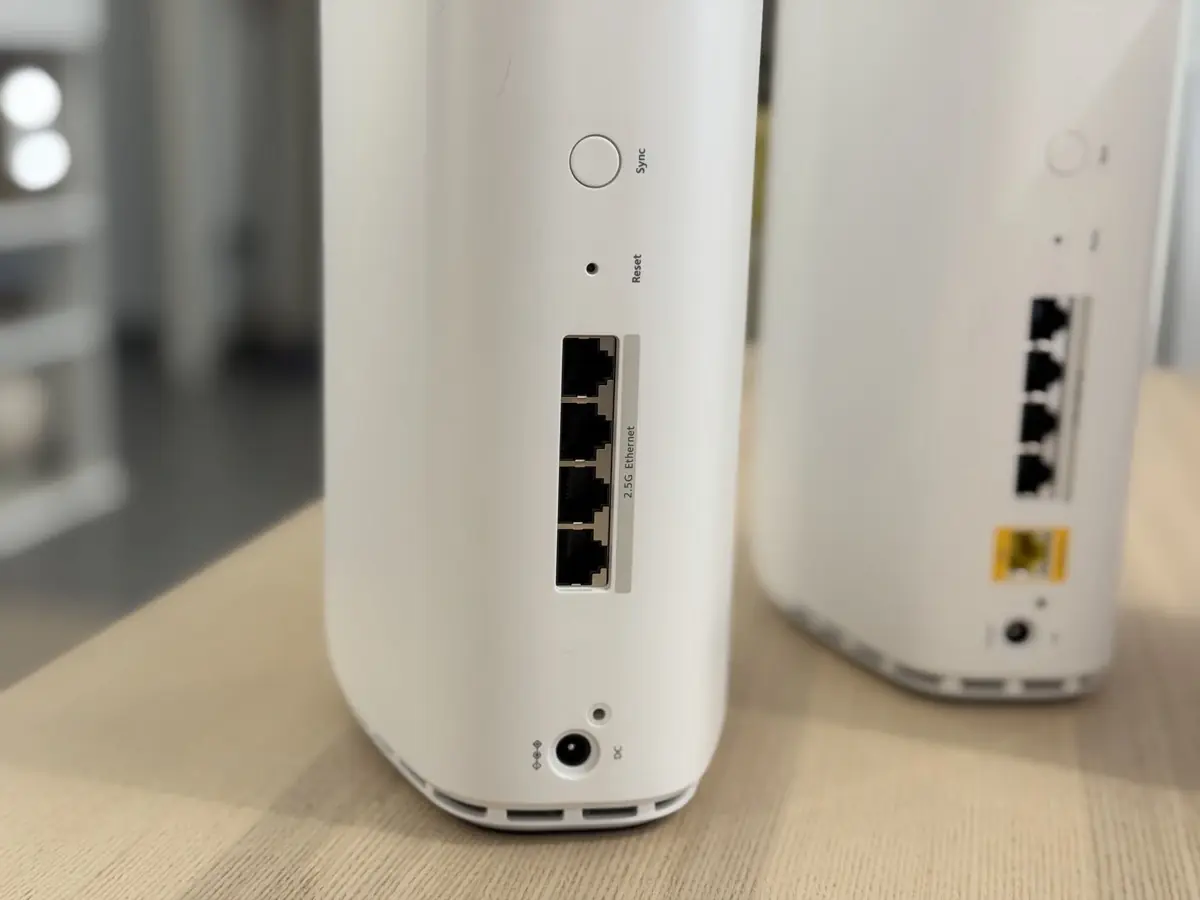
The FCC has approved a critical waiver for Netgear, making it the first vendor cleared to sell new consumer routers under strict cybersecurity rules.

A targeted cyberattack on French museums reveals a shift in digital warfare, moving from corporate data to the fragility of cultural logistics.

New research reveals how hackers can use drones to remotely shut down solar installations by exploiting the communication signals between panels and the grid.

Anthropic just dropped Claude 4.7 Opus. For developers, this isn't just a minor patch—it is a significant leap in codebase reasoning and complex debugging.

Learn how small-scale attackers are using dedicated hardware to bypass digital security and target users directly via physical proximity.

When a cyberattack parlayed through a ticketing vendor paralyzes a major museum, it signals a deeper shift in how we must protect cultural heritage in a digital-first economy.

Automatic Wi-Fi connections expose sensitive data to attackers. Learn how to disable this feature and protect your mobile privacy.

A look at Prime Video's new thriller Intraçables and why its portrayal of tech falls short for a developer audience.