
While security teams hunt for zero-day exploits, the 'Snow' group is simply overwhelming the human brain. This is social engineering at scale.

A deep explore the unit economics of funeral fraud and the dark business models targeting families during their highest period of cognitive load.

A deep explore why local governments are finally pricing in digital risk and what it means for the cybersecurity market.

Twelve million accounts exposed and a late response. France’s digital ID strategy is facing its most embarrassing stress test yet.

France is facing an unprecedented wave of data breaches. We examine the technical and social reasons why this European hub has become a favorite target for hackers.

When fifty tourists ended up sleeping in stairwells after booking through a major platform, it exposed the fragile link between digital marketplaces and physical reality.

Anthropic's latest security-focused model is terrifying the industry, but the real threat isn't the AI—it's the decades of lazy code it is about to expose.
A massive breach at France's ANTS has exposed 12 million records. Learn the technical implications and the specific steps required to secure your digital identity.
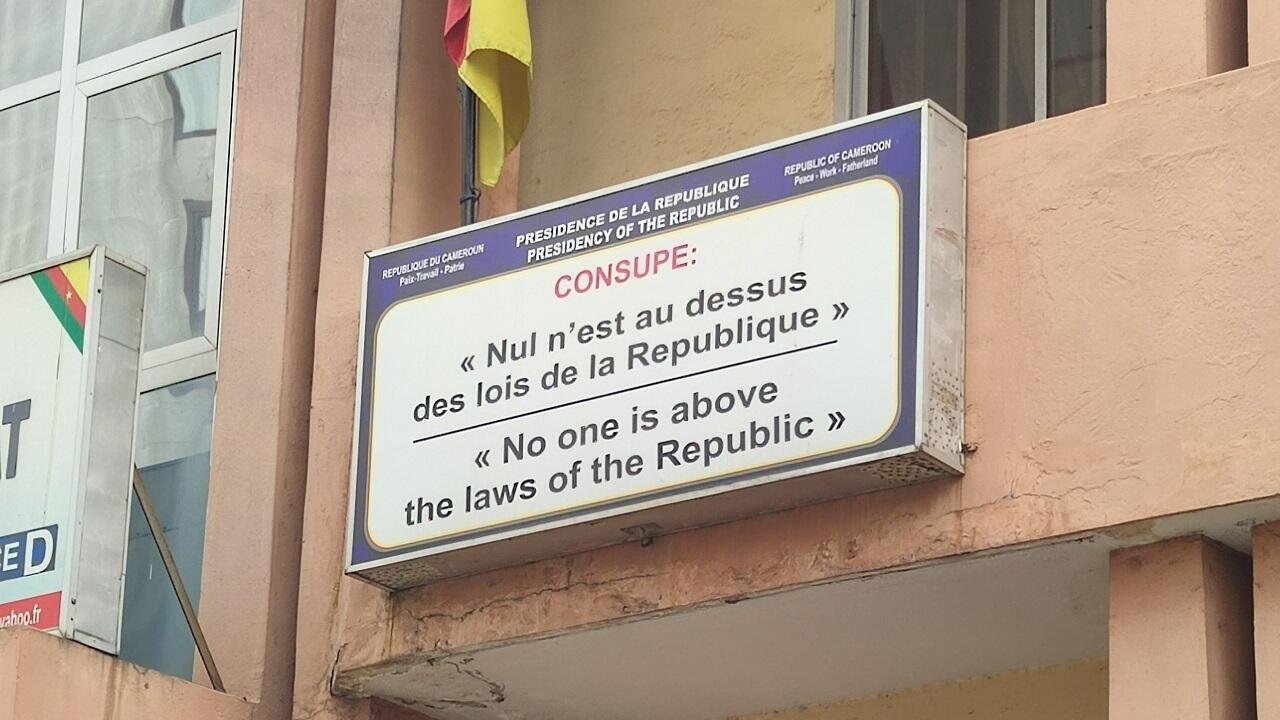
Analyzing the legal summons of Georges-Gilbert Baongla and its implications for Cameroon's political stability and presidential succession.

When the encrypted bubbles of Signal began to burst for German lawmakers, it revealed a new fragility in the quiet corners of European diplomacy.

Google shifts its security strategy to autonomous AI agents as human analysts fall behind the speed of automated cyberattacks.

A massive cyberattack on German lawmakers highlights why deep security isn't just for governments—it's a requirement for any scaling product.