
A major cyberattack on France's National Museum of Natural History shows that the real damage isn't just lost data—it is the administrative paralysis that follows.

A security researcher has disclosed three zero-day vulnerabilities in Microsoft Defender, leaving over a billion Windows users vulnerable to potential attacks.

Switzerland's top commander admits the nation faces significant vulnerabilities in air defense amid rising geopolitical tensions and hybrid warfare threats.
Data from Singapore reveals a paradox: high societal trust and civic compliance are becoming the primary vulnerabilities exploited by sophisticated digital scammers.

A new vulnerability in Adobe Acrobat is allowing hackers to compromise systems through simple documents. Learn how to stay safe.

CyberGhost is flexing a massive 12,000-server fleet for pennies, but a closer look at the infrastructure reveals the hidden costs of aggressive scaling.

As Anthropic prepares to release its most potent model yet, security experts scramble to determine if we are ready for an AI that knows too much about our digital flaws.
A third-party audit confirms DuckDuckGo's VPN collects zero identifies, marking a shift in how privacy-first companies handle network traffic.

A failed hack targeting Rockstar Games backfired, erasing 200,000 dollars in demands while boosting market valuation by a staggering 1 billion dollars.

CISA data reveals that hackers are still successfully exploiting a 14-year-old Microsoft flaw to deploy ransomware across enterprise networks.
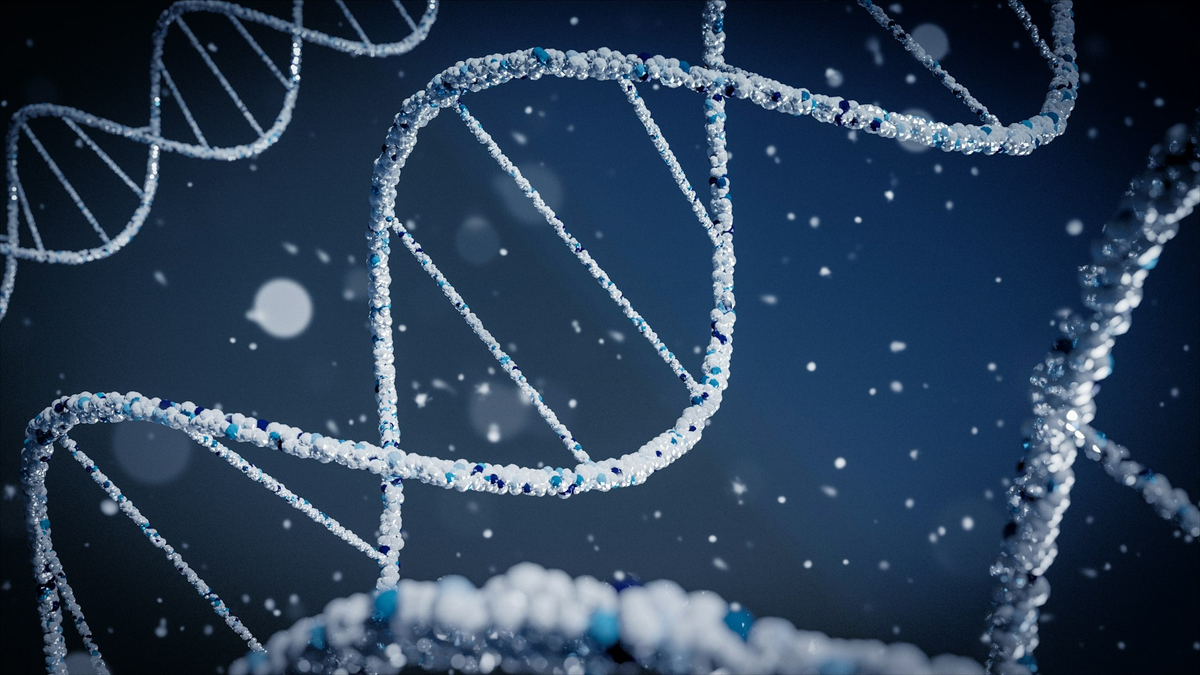
France and Japan have successfully tested DNA-based encryption, moving security from binary logic to biological permanence.
A recent security bypass of the EU's age verification pilot reveals the massive technical gap between policy and practical privacy.