
A deep explore Kratos, the PhaaS toolkit lowering the barrier for sophisticated cyberattacks targeting global enterprise infrastructure.

Intelligence reports reveal a surge in data breaches led by minors, highlighting a shift toward youth-driven cybercrime syndicates.

New data suggests the stereotypical elite hacker is a fantasy. The reality is younger, lonelier, and far more interested in social status than complex code.

The French government's long-delayed digital shield aims to block malicious websites in real-time, targeting phishing and online fraud attempts.
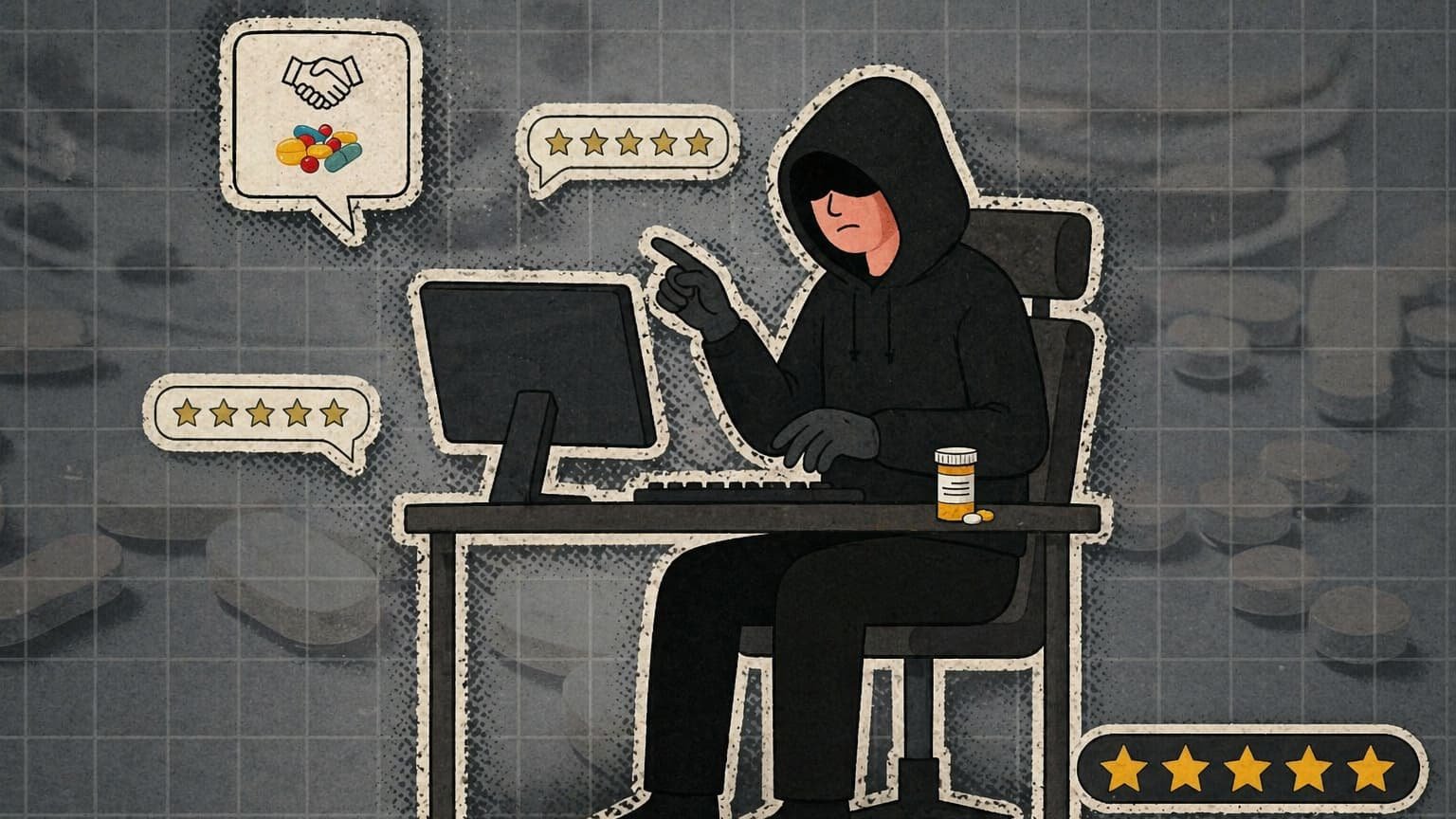
Drug traffickers are ditching the street corner for CRM systems and customer reviews. It's not a trend; it's a structural shift in how illegal goods move.

Surfshark One is moving beyond the VPN to build an all-in-one security platform. Here is why the bundle is the ultimate weapon against churn and legacy incumbents.

The FFBB's recent data breach of 2 million records reveals a systemic failure in how sporting bodies handle sensitive identity data.

Meta is reportedly tracking mouse movements and keystrokes of its US staff to feed the very AI models designed to automate their roles.

A fifteen-year-old’s breach of the French ANTS portal reveals that the real threat to national security isn't state actors, but the shifting geography of technical curiosity.

Shopping events like French Days bring out the best deals and the worst digital threats. Learn how to protect your data and your wallet.

In the shadow of a two-month internet blackout, Iranians are rediscovering the fragile texture of a life lived entirely offline.

A deep look into the IDOR vulnerability behind the ANTS breach and why logic failures are the new frontier of cybersecurity risks.