
Georges-Gilbert Baongla's legal push for DNA testing is more than a family feud; it is a direct challenge to the political and economic stability of Cameroon.

Total digital protection no longer requires a premium subscription; the architecture of modern security has turned free tools into high-performance assets.

Email is the primary entry point for 90% of cyberattacks. Learn to spot the subtle signs of a compromise and secure your data before the damage spreads.
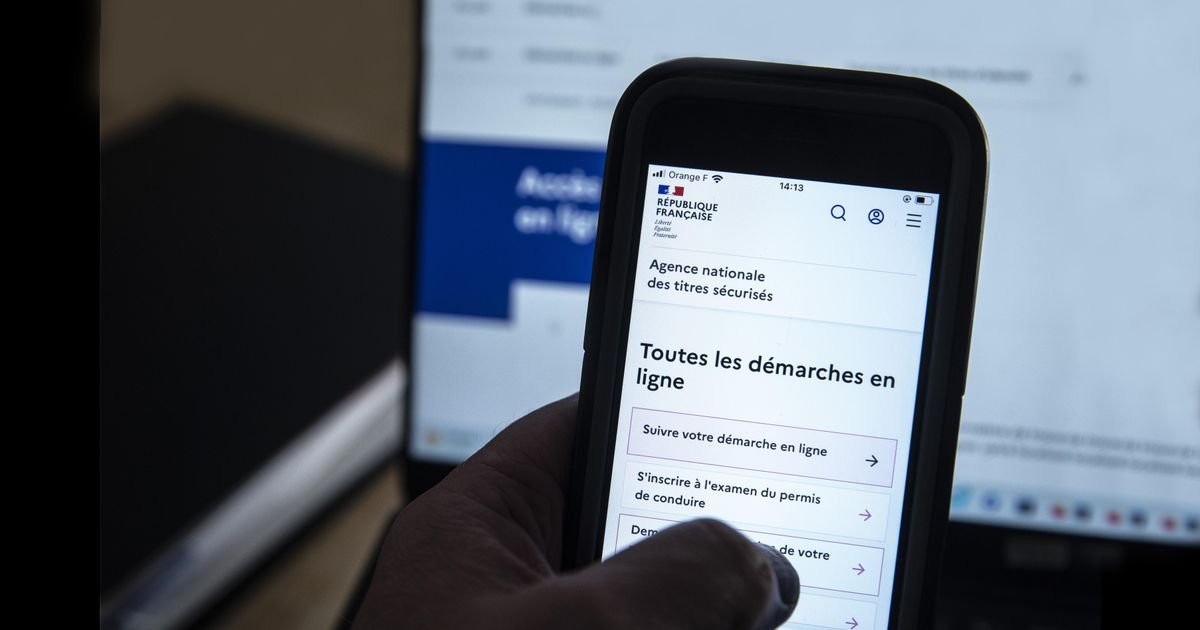
Government-scale breaches at ANTS and France Travail show that legacy infrastructure is failing. Here is how to protect your own user data.

As digital threats become more personal, Norton 360 Advanced offers a sprawling safety net for the modern multi-device household.

Despite a massive law enforcement takedown in June 2024, the controversial chat platform Coco has reappeared, exposing critical gaps in digital border controls.

New developments in AI security capabilities are narrowing the gap between human experts and machines. Here is how it changes digital safety.

A new alliance between cybersecurity giants and AI pioneers seeks to illuminate the blind spots that human eyes and standard code can no longer detect.

A massive leak involving top athletes like Neymar and Son Heung-min reveals critical gaps in how sports organizations handle sensitive identity data.

A massive leak involving icons like Neymar and Gianni Infantino exposes the vulnerability of the sports world's digital infrastructure.

France's Education Ministry is a massive honeypot for hackers. It's time to stop treating state-level data theft as an inevitability and call it what it is: neglect.

A deep look into how social media platforms have turned digital proximity into a multi-billion dollar vulnerability for the modern American consumer.