
Discover how Armenia's approach to democratic defense is providing European leaders with a new manual for resisting external political interference.

A massive data breach at Bouygues Telecom has exposed the personal details of 4.5 million users, raising fresh concerns about digital security.

Proton Mail introduces post-quantum cryptography to prevent the future decryption of today's private conversations.

A global Facebook breach using Google's own infrastructure reveals the hidden frailty of the modern web: the metadata we leave behind.

Financial reports from Versailles Hospital reveal that a single cyberattack in 2022 created a permanent fiscal deficit that legacy IT systems cannot outrun.

A fake petition claiming 14 million signatures for Mbappé’s exit reveals the low cost of manipulating sports sentiment and market perception.

As Swiss radiology networks face recurring breaches, we examine the systemic fragility of high-value diagnostic data in a connected age.
A major supply chain attack targeting Daemon Tools highlights critical vulnerabilities in software distribution and the risks of trusted vendor compromise.

A security breach at BNP Paribas Personal Finance has exposed thousands of customer email addresses, raising concerns over targeted phishing campaigns.

Ever answer a call only to hear dead air? It is not a glitch; it is the sound of a sophisticated algorithm profiling your life.
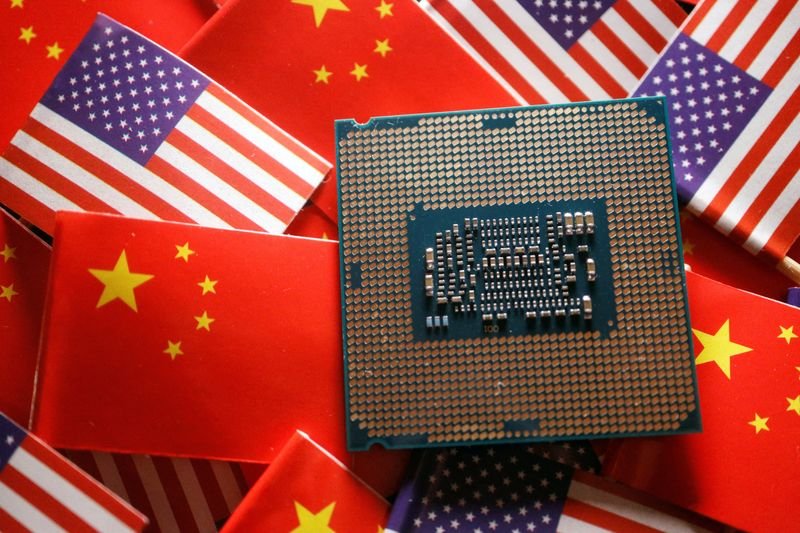
A quiet shift is happening in global diplomacy as the U.S. and China prepare to sit across the table to discuss the future of artificial intelligence.
French authorities are uncovering a startling trend: the most effective data thieves aren't seasoned pros, they're teenagers working from their bedrooms.