A surge in massive data breaches has French lawmakers demanding a Senate inquiry into the country's fragile digital defenses.
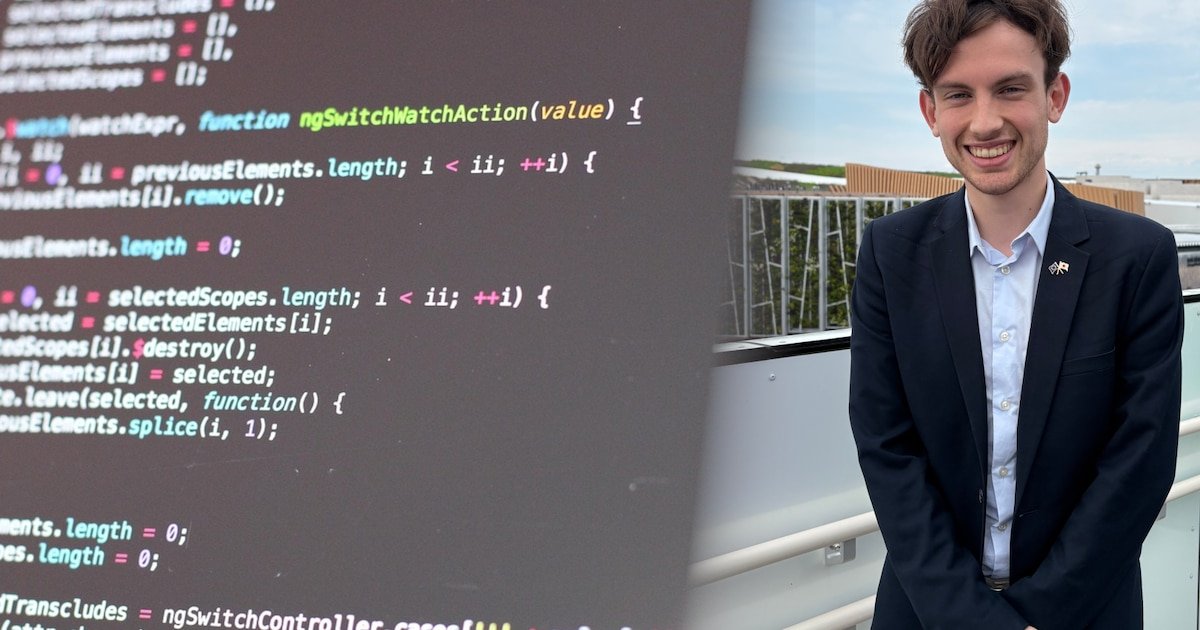
How Andrew Willems turned a 2022 startup into a global venture spanning from the streets of Belgium to the heart of Tokyo and New York.

Viral warnings claim scammers use silent phone calls to steal your voice. We investigate whether this is a technical reality or just effective engagement bait.

A massive leak at Canvas reveals the terrifying vulnerability of centralizing student data in a single software ecosystem.

A bug hidden for years in a SQLite database was finally cracked, not by a human genius, but by an LLM trained to hunt for flaws.

A recent shutdown at a major pharmaceutical plant reveals why digital security is no longer just an IT issue, but a fundamental pillar of physical manufacturing.

National security agencies are pushing a low-tech fix for high-tech surveillance, but can a simple restart really stop modern spyware?

AI is lowering the barrier for sophisticated cyberattacks. Here is how your team can defend against automated phishing and faster exploit cycles.

Portable cell towers are bypassing carrier security to inject phishing links directly into phones. Here is the technical debt making it possible.

A security breach at Bouygues Telecom has compromised an internal management tool, exposing sensitive customer information to unauthorized access.

Regulators are moving from theory to enforcement. Here is why the latest legal actions against Chatiw and Motherless matter for your platform's liability.
A recent cyberattack has exposed the contact details of thousands of political supporters. Here is what happened and how to protect yourself.