
A French Gendarme faces trial for child pornography, sparking a debate on institutional transparency and the risks of unchecked authority in local jurisdictions.

Cal.com's sudden shift to a restrictive license reveals a growing anxiety among developers who fear their work is becoming fuel for AI competitors.
A recent security incident at Basic-Fit has exposed member data. Here is a clear breakdown of what happened and how to protect your digital identity.

Barclays CEO CS Venkatakrishnan warns that Anthropic's latest models are no longer just productivity tools—they are becoming sophisticated blueprints for a new era of cyber warfare.

As Iran enters its 50th day of an unprecedented internet shutdown, we examine the technical and economic toll of a nation disconnected by design.

French courts are dismantling the 'arms dealer' defense of NSO Group. Discover why this legal move signals the end of the boutique cyber-intelligence business model.

Financial institutions claim your IBAN is for deposits only, but a growing black market for banking data suggests your account is more exposed than they admit.
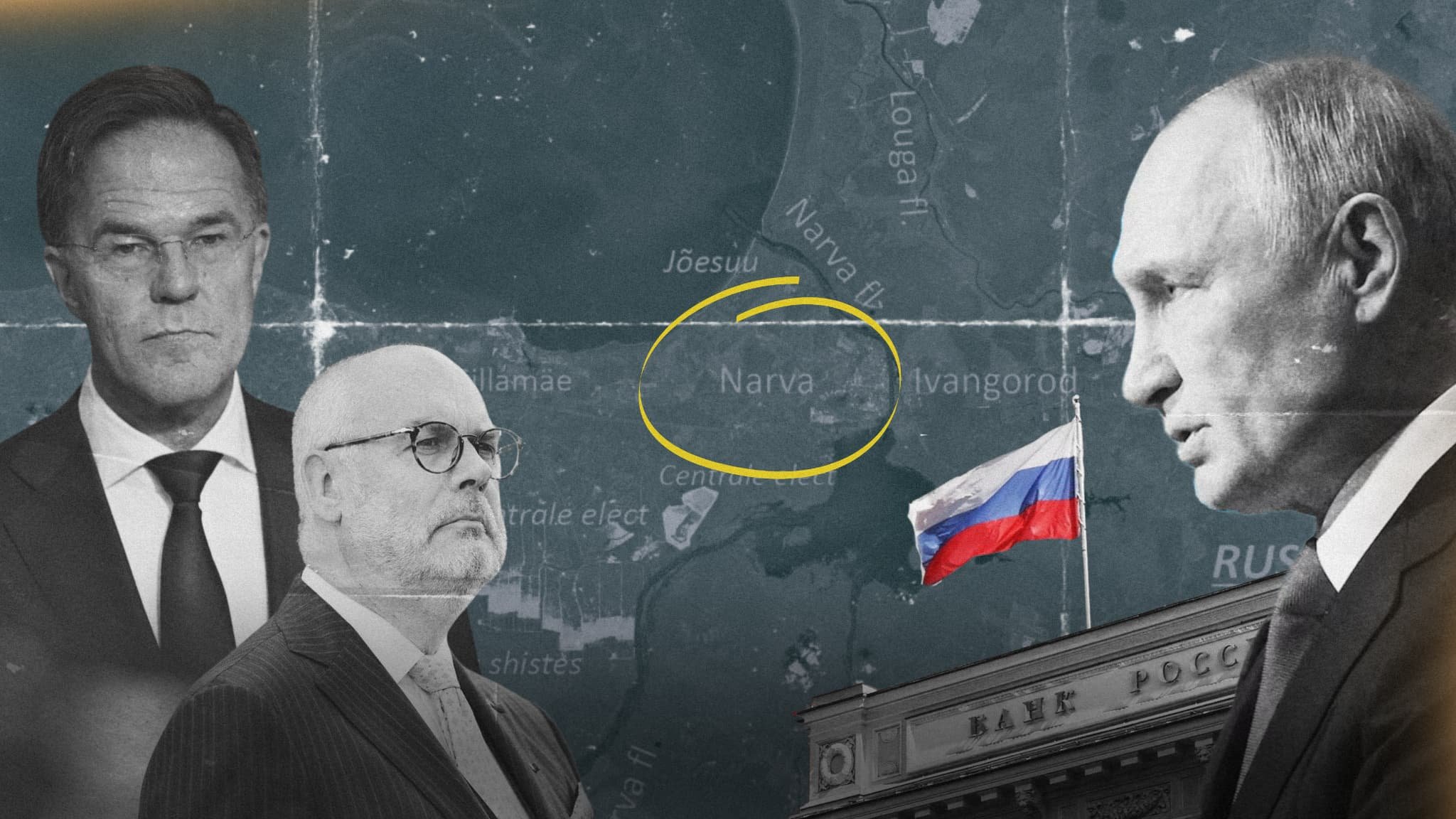
Russia's fake Narva People's Republic reveals a shift in geopolitical strategy: why manufacture weapons when you can manufacture doubt for the price of a SaaS subscription?

Elon Musk's summons by French authorities signals a new chapter in the struggle between digital sovereignty and Silicon Valley’s libertarian ideals.

When French TV icon Olivier Minne lost his digital identity to hackers, he discovered a hollowed-out platform where nobody was left to answer the call.

Security researchers identified over 100 Chrome extensions used to steal user data and hijack browser sessions in a coordinated Russian campaign.
A massive breach of the French Education Ministry's database exposes the vulnerability of centralized public sector data management.