
Bouygues Telecom has suffered its second major breach in a year, proving that your personal data is merely collateral damage in the race for market share.

A quiet attack on a French municipal police force reveals a massive vulnerability in how local governments secure sensitive citizen identity and vehicle data.

A massive leak at SFR Business exposes how legacy systems and third-party access points create critical vulnerabilities for enterprise data.
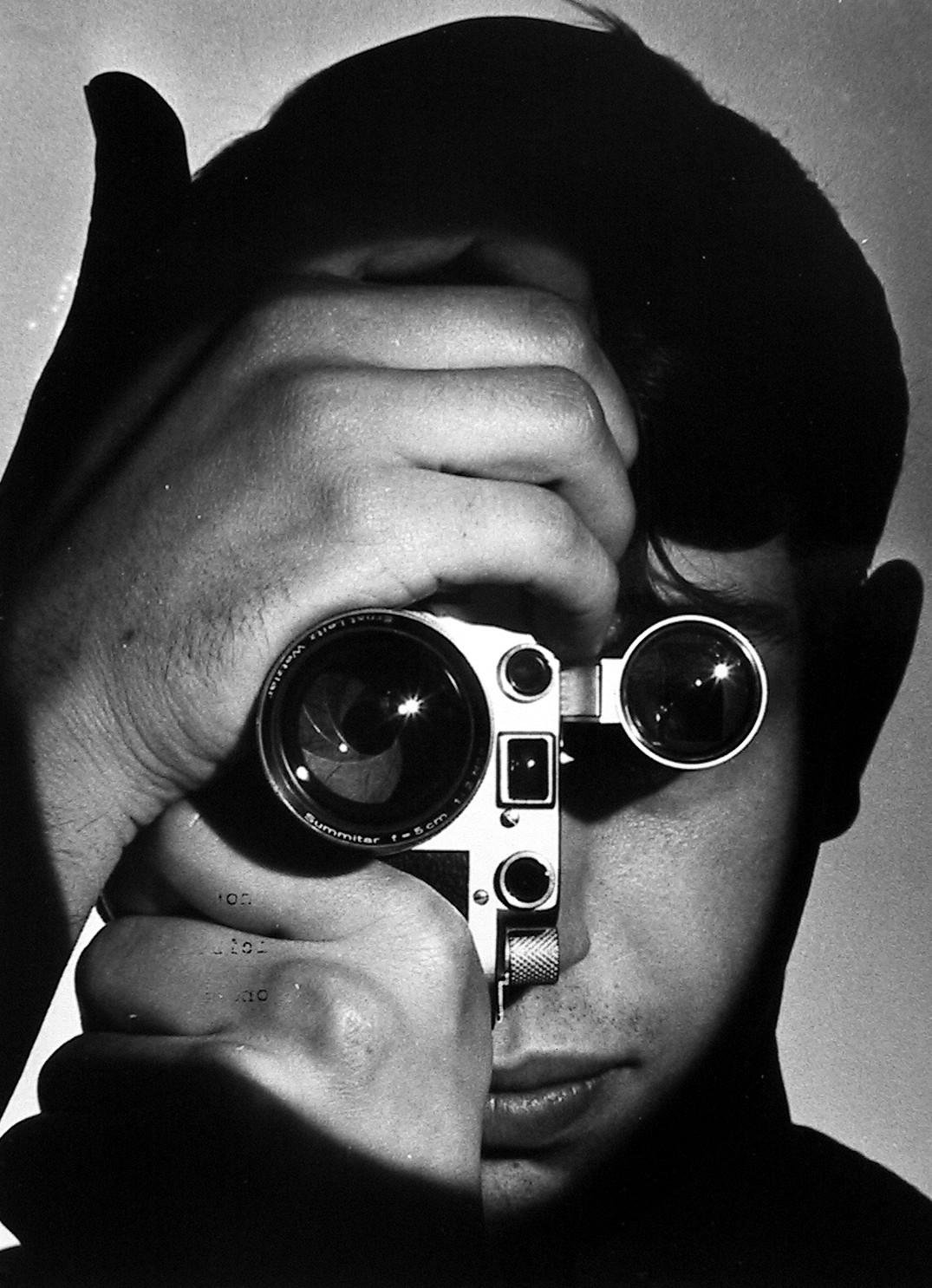
When cyberattacks strike cultural institutions like L’Œil de la Photographie, it signals a shift from data theft to the erosion of shared digital memory.

OpenAI's response to Anthropic's Claude Mythos reveals a desperate race to secure the digital perimeter, but at what cost to privacy and open architecture?

When the Minister for AI visits a software giant in Montpellier, the narrative is about European leadership. The reality is a story of aggressive consolidation and vertical control.

Microsoft just patched 120 security flaws, dealing with a massive backlog of digital vulnerabilities before they could be exploited in the wild.

Senegal's Treasury is the third major state institution hit by hackers in six months. We analyze the fiscal risk and the looming threat to West African digital trust.

Legal frameworks define when remote workers are financially responsible for data breaches and hardware damage occurring outside the office.

Google's Threat Analysis Group detected a milestone event where attackers utilized AI to exploit a previously unknown software vulnerability.

Europe's silent trade in surveillance tools mirrors the double standards of history's great trading empires, trading democratic values for market dominance.

A Paris investigation into an open-access forum reveals the unsettling visibility of modern digital deviance and the challenges of policing the public web.