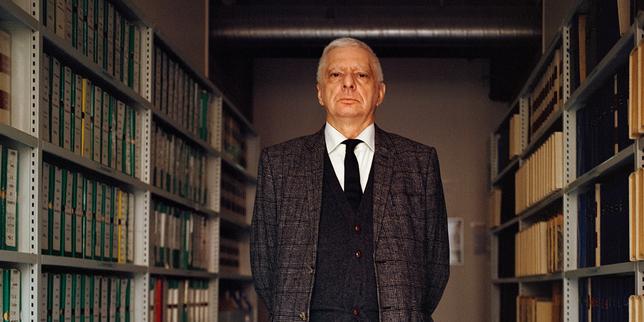
Political scientist Jean-Yves Camus spent decades studying the far-right. Now, critics wonder if the expert has become too close to the subjects he monitors.

When Hachette skips the traditional book fair to host its own festival, it signals a shift from broad discovery to curated ecosystems in the attention economy.

Despite a thirty-year hiatus and a criminal record, Alain Carignon's polling numbers prove that in politics, as in tech, distribution beats product quality.

Inside the investigation into France's 'Preservation Schools,' where the state used the language of protection to justify the indefinite detention of young women.

Montreal's latest crackdown on digital extortion rings reveals a disturbing shift: organized crime has moved to the cloud, and the law is finally catching up.

A look into the human mechanics of a phishing ring that drained bank accounts across Belgium and the police operation that finally closed the circuit.

A new exploit dubbed DarkSword is bypassing iOS security with a single click, proving that even the most secure smartphones are vulnerable to invisible threats.

Inside the unseen digital conflict where Iranian cyber units target the physical infrastructure and social trust of their adversaries.

A technical look at how Kim Dotcom built a massive file-sharing empire and the infrastructure challenges of scaling a site to 4% of total internet traffic.

As tensions rise, Iranian state-sponsored actors are shifting from blunt disruptions to sophisticated identity theft. Is your infrastructure prepared for the long game?

A new wave of cyberattacks uses hidden code within standard web pages to bypass security filters. Here is how it works and how to stay safe.

Phishing attacks impersonating the French Treasury are surging. Here is how to protect your company's data and financial credentials from these sophisticated tax-season frauds.