Why the DRC's New Cyberdefense Council Matters for Tech Operations in Africa
How does the CNC affect your digital infrastructure?
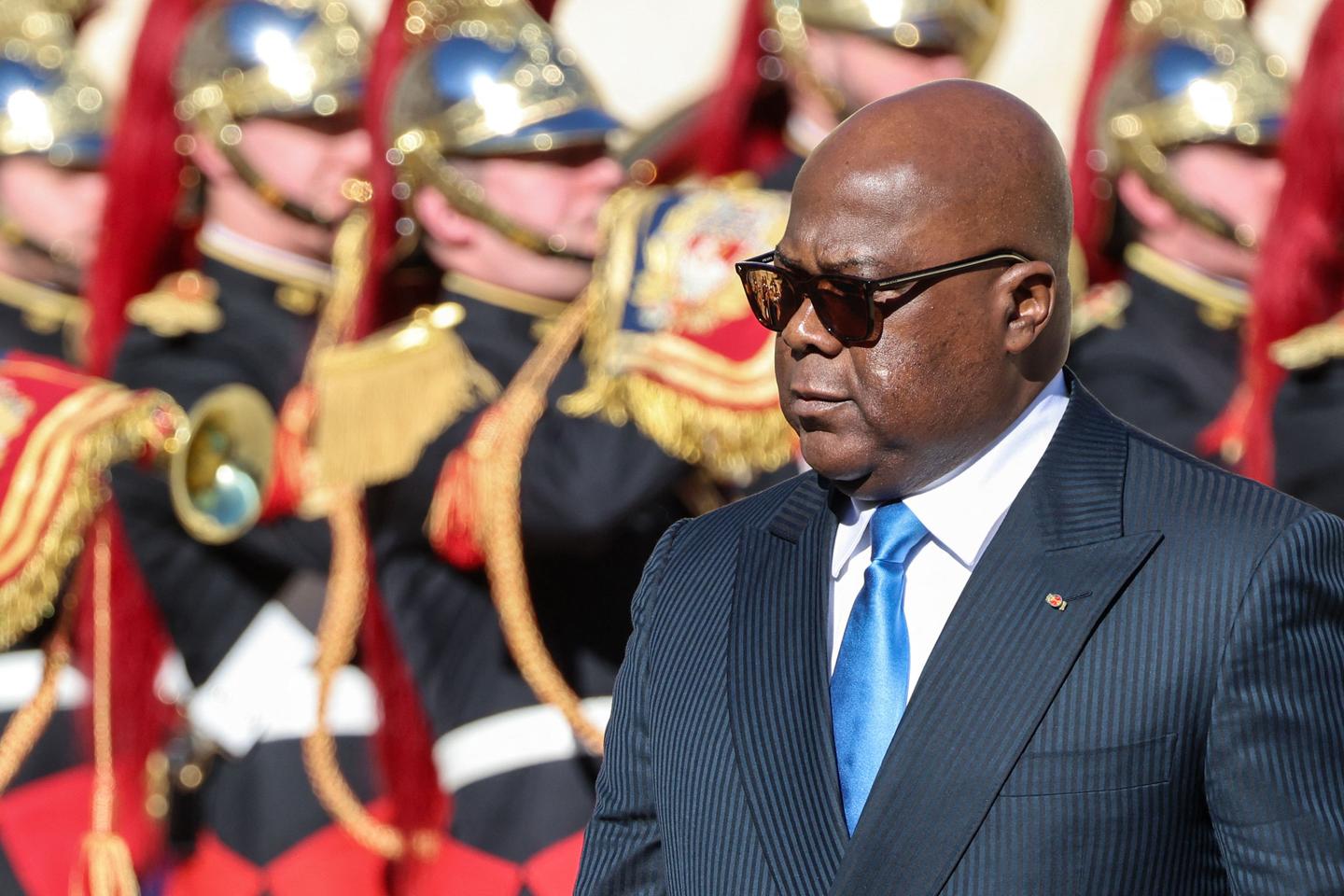
If you are operating a digital platform or managing data within the Democratic Republic of Congo, the regulatory environment just became significantly more complex. The establishment of the National Cyberdefense Council (CNC) under the presidency of Felix Tshisekedi marks a shift from traditional infrastructure protection to active digital surveillance. For builders, this means the risk profile of hosting local data or providing encrypted communication services has changed overnight.
The CNC is not just another bureaucratic agency. It operates with a direct mandate from the head of state, granting it authority that often bypasses standard judicial oversight. While the official goal is to protect against external cyber threats and terrorism, the practical application has increasingly focused on internal monitoring. If your product relies on user privacy or secure data transmission, you need to account for a state actor with the legal right to demand access to your systems under the guise of national security.
What are the technical risks of overreaching oversight?
Engineering teams usually build for security, but the CNC introduces a human element of risk that code cannot always solve. Reports indicate the agency uses aggressive methods to monitor digital traffic and suppress dissent. This creates a precarious situation for developers who must balance local compliance with international data protection standards like GDPR or CCPA.
- Backdoor Demands: There is a heightened risk of state requests for administrative access to databases or communication logs.
- Infrastructure Vulnerability: Centralized surveillance often creates new security holes that third-party hackers can exploit.
- Data Residency Issues: Storing data on local servers in Kinshasa now involves a trade-off between latency and the physical security of your hardware.
- Operational Continuity: Sudden administrative orders to shut down services or hand over encryption keys can disrupt your uptime and damage user trust.
The lack of a clear legal framework defining the boundaries of the CNC means that 'cyberdefense' is a flexible term. In practice, this allows the agency to intercept private communications and track geolocation data without a warrant. For a startup founder or a CTO, this translates to a liability that must be addressed in your terms of service and security architecture.
How should you adapt your security posture?
Ignoring the political reality of the CNC is a recipe for a compliance disaster. You need to treat state-level surveillance as a persistent threat model rather than a theoretical edge case. This starts with minimizing the amount of sensitive data you collect in the first place. If you don't have the data, you can't be forced to hand it over.
- Implement End-to-End Encryption: Ensure that you do not hold the keys to user conversations or sensitive files.
- Audit Your Access Logs: Know exactly who is accessing your production environment and from where.
- Legal Shielding: Consult with local legal experts to understand the specific triggers that allow the CNC to seize equipment or data.
- Zero-Knowledge Architecture: Move toward systems where the server knows as little as possible about the data it stores.
The expansion of the CNC's power suggests that the DRC is following a broader regional trend of tightening control over the internet. As a builder, your priority is protecting your users. This requires a proactive approach to technical sovereignty and a clear-eyed understanding of the local political space. Watch for new decrees regarding ISP cooperation, as these usually signal the next phase of data collection efforts.
Planificateur social media — LinkedIn, X, Instagram, TikTok, YouTube






























