The Industrialization of Smishing: How AI-Generated Visuals are Driving Package Scams
The 15% Conversion Jump in Personalized Fraud
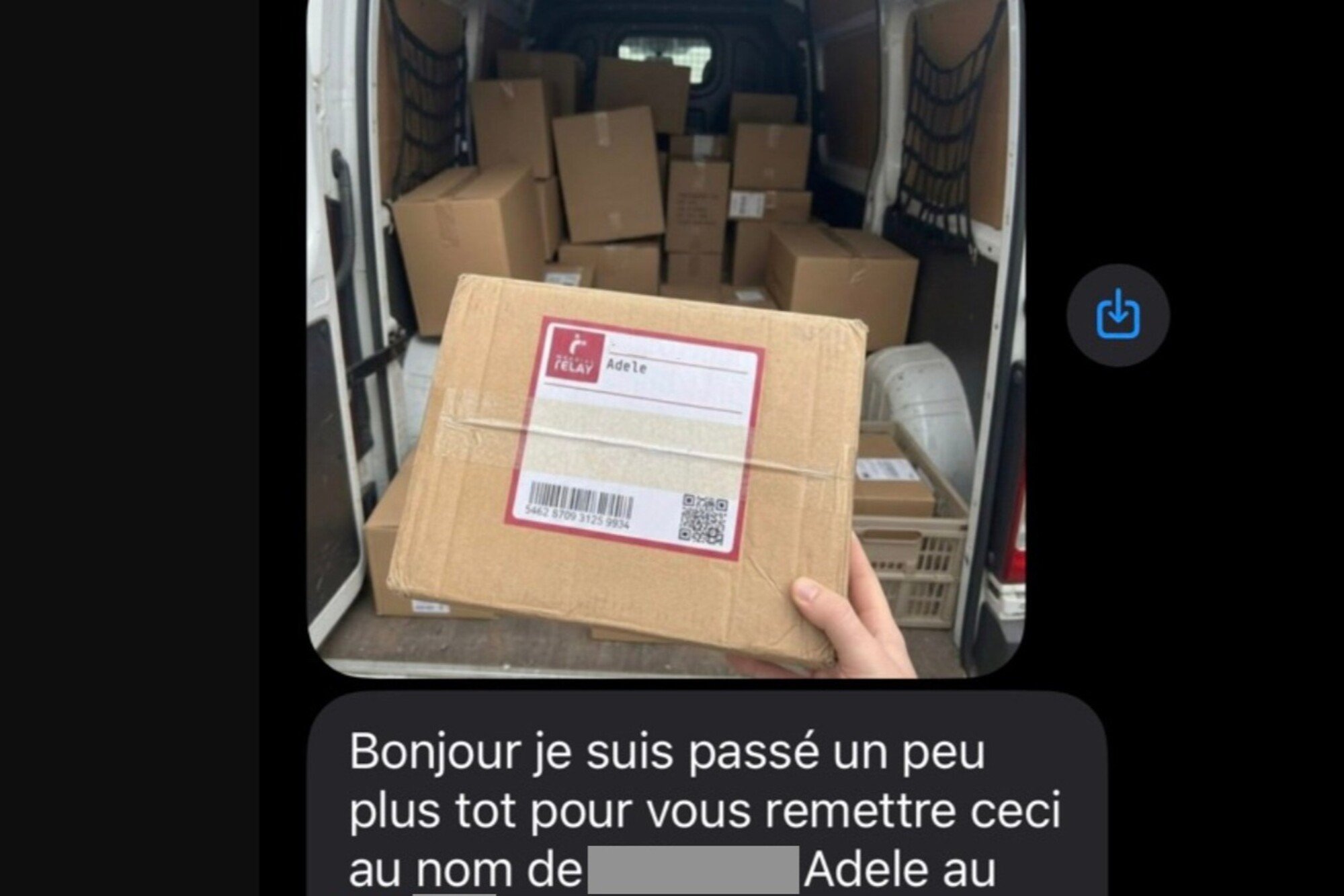
Cybersecurity data shows that traditional phishing emails typically yield a 1% to 3% click-through rate, but the integration of generative AI visuals is pushing those numbers significantly higher. Threat actors have moved beyond generic 'delivery failed' templates to a sophisticated pipeline of automated image manipulation. By superimposing a target's specific name and address onto a digital photograph of a cardboard box, attackers are neutralizing the primary defense of modern internet users: skepticism of generic content.
This shift represents a transition from broad-spectrum attacks to high-precision social engineering. The psychological friction of receiving a text message about a missing parcel is almost entirely removed when the message includes a high-resolution image of a box physically labeled with the recipient's details. Data suggests this level of personalization can increase victim engagement by as much as 350% compared to standard text-only SMS scams.
The Architecture of an Automated Visual Scam
The technical execution of these campaigns relies on three distinct layers of automation that work in sequence. This is no longer a manual process where a hacker uses Photoshop for each victim; it is a factory-scale operation. The workflow typically follows this order:
- Data Ingestion: Attackers purchase leaked databases from recent e-commerce breaches containing names, phone numbers, and physical addresses.
- Dynamic Image Rendering: Scripted tools use AI models to overlay the stolen text onto a base image of a shipping container, adjusting for perspective, lighting, and texture to make the label appear authentic.
- Automated Distribution: Smishing (SMS phishing) gateways send the personalized image and a tracking link to the victim, often spoofing the sender ID of legitimate logistics firms like FedEx, DHL, or La Poste.
By using OpenCV or similar image processing libraries combined with generative fills, hackers create a sense of urgency. The recipient sees their own name on a physical object, which triggers a localized 'ownership effect,' making them more likely to pay a small 'redelivery fee'—the primary mechanism for stealing credit card credentials.
Economic Incentives and the Cost of Defense
The cost to generate these personalized images has plummeted to near zero. While a human designer would take 10 minutes to create a convincing fake, an AI-driven script can produce 10,000 unique images per hour for the price of a few kilowatt-hours of compute time. This efficiency makes the 'long tail' of small-dollar fraud highly profitable for criminal organizations.
"We are seeing a move away from the 'Nigerian Prince' era of obvious errors toward a period of hyper-realism where the human eye can no longer distinguish between a system-generated notification and a criminal lure," noted a senior analyst at a leading European cybersecurity firm.
Telecommunications providers are currently struggling to filter these messages because the content of the image is opaque to traditional text-based spam filters. While Natural Language Processing (NLP) can flag suspicious keywords in a text, analyzing the metadata and pixel-level consistency of every image sent via MMS requires a level of compute power that most carriers are not yet willing to deploy at the network edge.
Expect to see a 40% increase in these visual-based SMS attacks through the next two fiscal quarters as the underlying software kits become more accessible on the dark web. By early 2025, the standard for digital verification will likely shift toward mandatory app-based notifications, as the SMS protocol becomes too compromised by AI-generated visual deception to remain a reliable channel for logistics communication.
OCR — Texte depuis image — Extraction intelligente par IA






























