The Glass Door Problem: Why Verifying Age Online Is Harder Than It Looks
The Anatomy of a Two-Minute Bypass
Most of us are used to the honor system online. When a website asks if you are over 18, you click a button, and you are in. The European Union recently attempted to replace this digital Pinky Swear with a more rigorous tool, but the first major trial hit a wall almost immediately.
Security researchers managed to circumvent the new age-verification application in roughly 120 seconds. This was not the result of a complex, high-resource cyberattack. Instead, it was a demonstration of how difficult it is to build a digital gate that is both secure enough to keep minors out and private enough to protect adults.
The flaw did not lie in the user's identification document itself, but in the way the application communicated with the server. By intercepting the data packet sent between the phone and the verification center, researchers could trick the system into believing a validation had occurred without ever providing proof.
Why We Cannot Just Use ID Cards
The core challenge of age verification is a concept called data minimization. In a perfect world, a website should only know a single binary fact about you: Are you over the threshold? It should not know your name, your address, or your exact birth date.
- Privacy risks: If every adult uploads their passport to a central database to access social media, that database becomes the world's most attractive target for identity thieves.
- Friction: Users generally abandon services that require more than a few clicks to get started.
- Technical fragmentation: Different countries use different standards for digital identity, making a universal 'Internet ID' a logistical nightmare.
The EU's pilot program attempted to use a zero-knowledge proof approach. This is a cryptographic method where one party can prove to another that a statement is true without revealing any additional information. While the theory is sound, the implementation in this specific app failed because the 'handshake' between the user and the service was not sufficiently encrypted.
The Trade-off Between Safety and Surveillance
Regulators are currently caught between two opposing forces. On one side is the urgent need to protect children from harmful content. On the other is the fundamental right to browse the internet without being tracked by a government-mandated identity layer.
The Middle Ground Technologies
Developers are currently testing three main ways to solve this without creating a surveillance state:
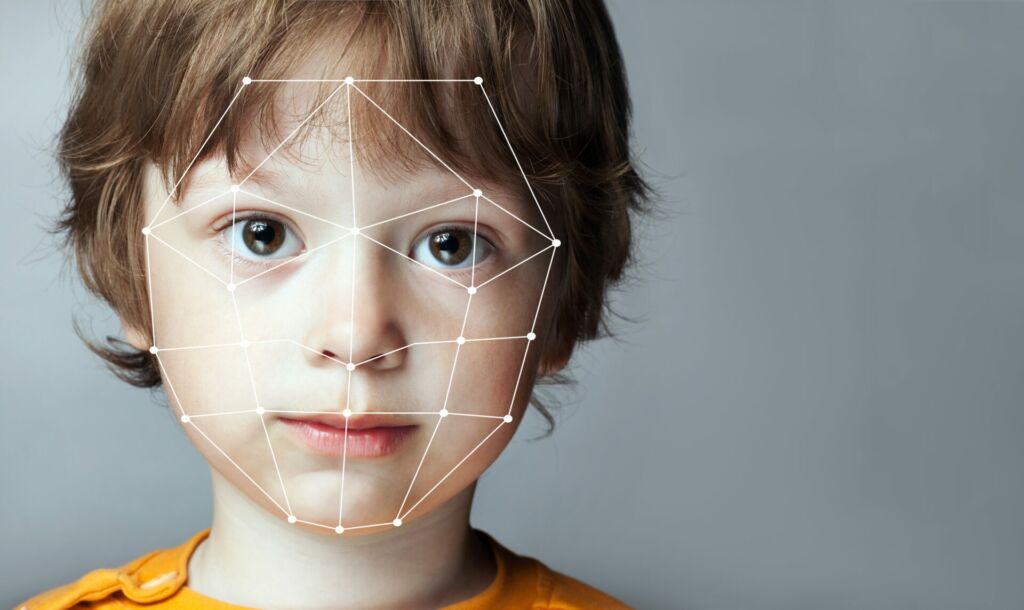
- Face Estimation: Using AI to analyze facial features via a camera. It does not identify who you are, only how old you likely are.
- Banking Verification: Using existing credit card or bank login data to confirm age, relying on the fact that banks have already done the heavy lifting of ID checks.
- Third-Party Oracles: Independent companies that verify your ID once and then issue a digital 'token' that you can use elsewhere without re-sharing your personal details.
The failure of the recent EU pilot serves as a reminder that policy cannot outpace technical reality. If a security system can be dismantled in the time it takes to brew a cup of coffee, it creates a false sense of security that is more dangerous than having no gate at all. For developers and founders, the lesson is clear: verification is not just about checking a box; it is about securing the entire pipeline of data transmission.
Now you know that the biggest hurdle in internet safety isn't identifying who is a child—it is doing so without compromising the privacy of every adult on the web.
Chat PDF avec l'IA — Posez des questions a vos documents






























