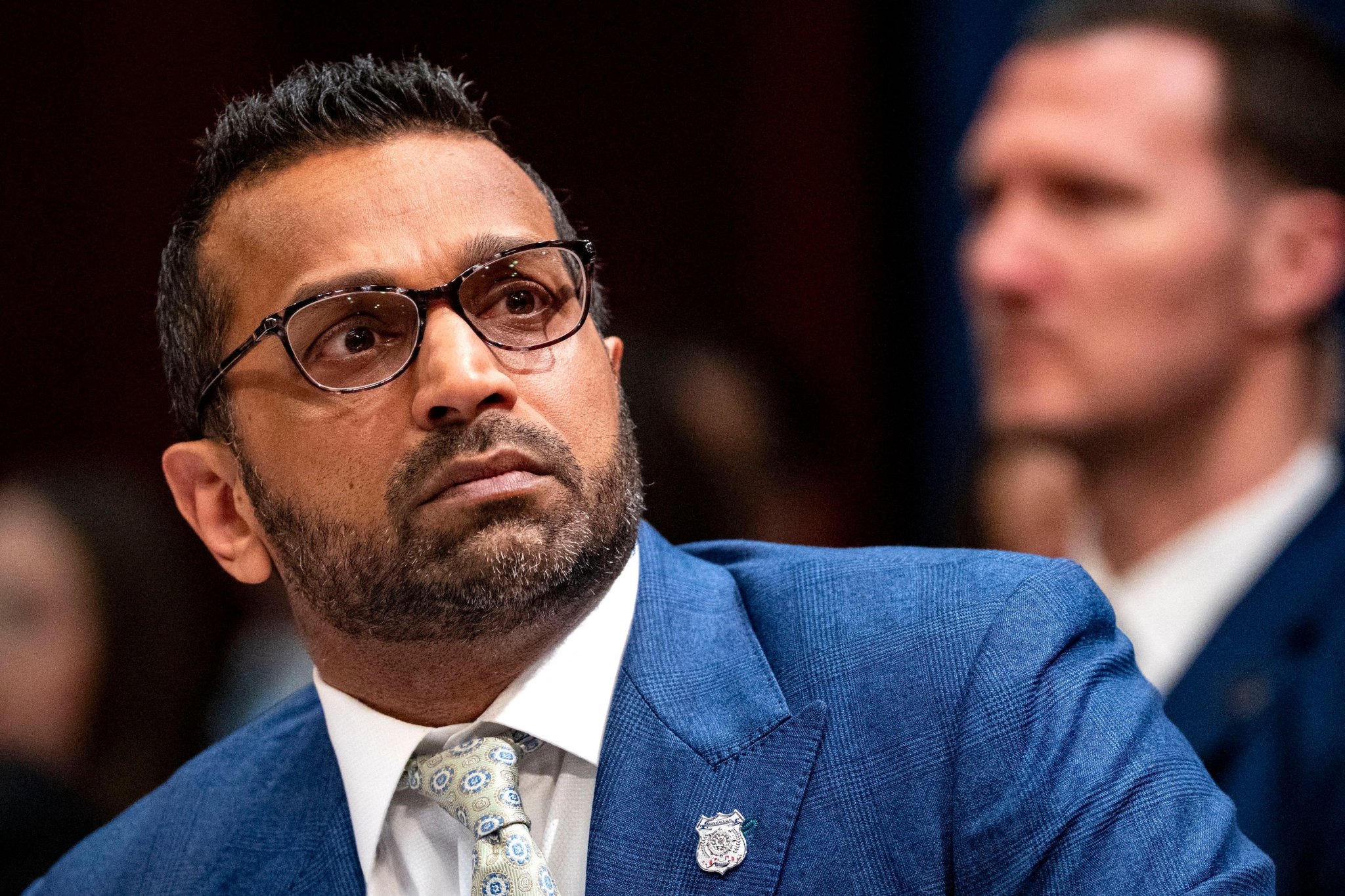
The FBI Security Breach: How Iranian Hackers Accessed Kash Patel’s Personal Data
State-Sponsored Actors Target the Top of the American Intelligence Pyramid
Recent intelligence reports confirm that Iranian state-sponsored hackers successfully breached the personal email accounts and digital storage of Kash Patel, the Director of the Federal Bureau of Investigation. This incident highlights a persistent vulnerability in the security protocols of high-ranking government officials who maintain digital footprints outside of classified networks. The breach resulted in the unauthorized acquisition of private correspondence and personal photographs, marking a significant escalation in the ongoing digital conflict between Tehran and Washington.
Data suggests this was not a random act of cybercrime but a calculated spear-phishing campaign designed to extract metadata and private communications for geopolitical gain. Security analysts at major cybersecurity firms have tracked similar patterns of behavior from groups linked to the Iranian ambitious Guard Corps (IRGC), who frequently target the inner circles of U.S. administrations. By bypassing standard enterprise-grade protections, the attackers exploited the relative weakness of personal authentication methods used by the Director.
The Mechanics of a High-Level Personal Data Compromise
The technical execution of the breach followed a sequence that has become increasingly common in statecraft. Attackers often spend months mapping the digital habits of a target before deploying a specific exploit. In this case, the sequence of the attack appears to have followed a three-step progression:
- Social Engineering: Hackers likely sent tailored messages that appeared to originate from trusted contacts within the political or legal community to gain initial entry.
- Credential Harvesting: Through the use of sophisticated fake login portals, the attackers obtained the login credentials for Patel’s non-government communication tools.
- Data Exfiltration: Once access was established, automated scripts were utilized to mirror the contents of the inbox and cloud storage before security alerts could be triggered.
The impact of this breach extends beyond the individual. When the head of a domestic intelligence agency is compromised, the data can be used to map out social networks, identify private associates, and potentially blackmail other government employees. While the FBI maintains that classified systems remained untouched, the psychological and strategic damage of such an intrusion is measurable in diplomatic capital and public trust.
Evaluating the Risks of Hybrid Digital Lives
This incident underscores the friction between the convenience of consumer technology and the rigorous requirements of national security. Government officials frequently use personal devices for scheduling or informal discussions, creating a secondary attack surface that is often less guarded than the official .gov infrastructure. Statistics from the 2023 Cybersecurity and Infrastructure Security Agency (CISA) reports indicate that 74% of all successful breaches involve a human element, such as social engineering or the misuse of personal credentials.
Iranian cyber units have shifted their focus toward these softer targets because the return on investment is higher. Breaking into a secured government server requires zero-day exploits that cost millions of dollars on the dark web. In contrast, compromising a personal email account requires only a well-crafted message and a moment of human error. This specific breach serves as a case study for why the distinction between private and professional digital life is becoming an unsustainable security model for those in power.
As we move toward the 2024-2025 fiscal year, expect the Department of Justice to mandate stricter 'air-gapping' for the personal devices of cabinet-level officials. The Iranian intelligence apparatus has demonstrated that no individual is too high-profile to be targeted, and the data harvested today will likely be used in disinformation campaigns or targeted leaks over the next eighteen months.
Planificateur social media — LinkedIn, X, Instagram, TikTok, YouTube






























