The Recursive Breach: Why the New York FBI Hack Signals the End of Opaque Intelligence
The Panopticon Flips: When the Watcher is Watched
In the late 19th century, Jeremy Bentham conceived of the Panopticon—a circular prison where a single guard could observe all inmates without them knowing if they were being watched. For decades, federal intelligence agencies functioned on a digital version of this architecture. They held the keys, the data, and the invisibility. But a recent intrusion into an FBI server in New York by a lone actor suggests that the walls of the Panopticon have become glass from both sides.
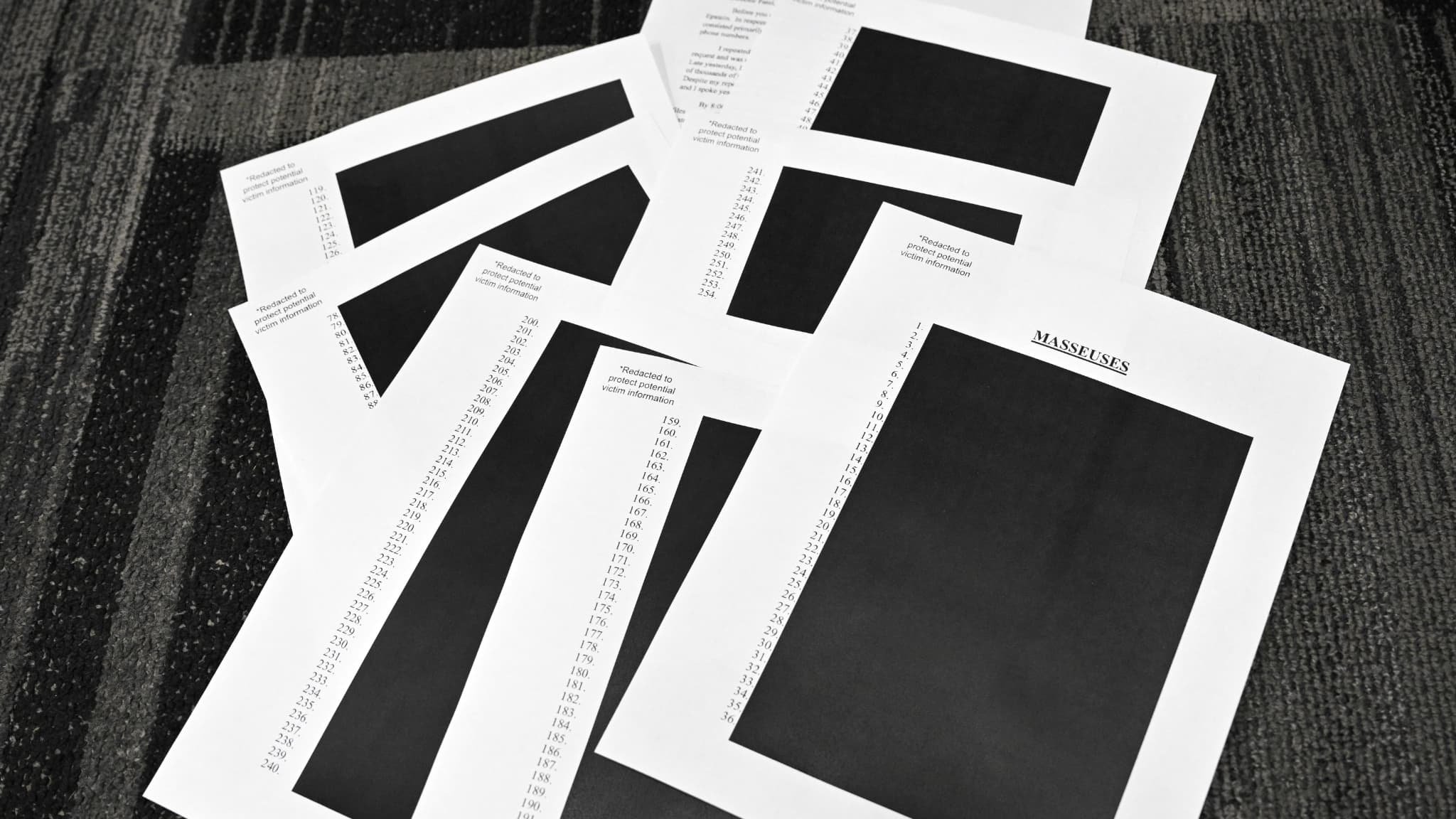
The breach did not involve a state-sponsored group or a sophisticated cyber-warfare unit. Instead, it was an accidental discovery by a hacker who stumbled upon a cache of files related to the Jeffrey Epstein investigation. The irony here is thick: the intruder was so disturbed by the contents of the server that they threatened to report the server owner to the FBInot realizing they had already breached the bureau itself. This incident reveals more than just a security lapse; it highlights a growing asymmetry in the digital age where institutional authority no longer guarantees data sanctity.
We are entering an era of 'recursive transparency.' When the entities tasked with global surveillance cannot maintain their own perimeters, the traditional hierarchy of information collapses. Historically, secrets were protected by physical distance and heavy steel. Today, they are protected by code that is increasingly porous. This event is a signal that the friction required to access the world's most sensitive secrets has dropped to an all-time low, regardless of the gatekeeper's pedigree.
The true vulnerability of modern intelligence lies not in the strength of the encryption, but in the assumption that the institution remains the sole arbiter of what remains hidden.
From Fortresses to Fluidity: The Infrastructure of Accountability
The FBI’s New York field office is arguably one of the most significant hubs of American law enforcement. That a hacker could dwell within its systems long enough to review sensitive case files suggests a shift in the nature of 'security.' We are moving away from a world of perimeter defense toward a world of constant, ambient risk. Think of it as the transition from a walled city to a biological organism; the skin is always being pierced, and survival depends on internal immune responses rather than external barriers.
This breach serves as a case study for startup founders and CTOs who believe their proprietary data is safe behind traditional cloud configurations. If an agency with the resources of the FBI can suffer an accidental infiltration, the concept of a 'secure server' becomes a polite fiction. The hacker’s reaction—moral outrage—adds a layer of human unpredictability to the tech stack. Data is no longer just bits; it is social currency that can be weaponized by anyone who finds it, often with motives that bypass financial gain in favor of chaotic justice.
Digital architecture must now account for the 'accidental whistleblower.' This is the individual who enters a system looking for one thing, finds another, and feels a civic duty to expose it. This creates a new type of liability for organizations. It is no longer enough to protect data from competitors; one must protect it from the moral judgment of the accidental visitor. The technical failure at the FBI is secondary to the reputational risk that followed, as the public once again questions the handling of high-profile evidence.
The Erosion of Institutional Trust
Trust in the 20th century was built on the competence of the institution. We trusted the bank because the vault was thick; we trusted the government because the files were classified. But in a networked society, competence is measured by the ability to manage complexity, and the FBI's failure here indicates a struggle to keep pace with the decentralization of expertise. When a rogue individual possesses more agility than a federal department, the power dynamic of the state begins to fray at the edges.
This incident will likely force a re-evaluation of how investigative data is siloed. We may see a move toward decentralized data storage or 'zero-knowledge' architectures where even the hosting agency cannot access the full scope of the material without multi-party authentication. The goal is to remove the 'single point of failure' that this New York server represented. In the future, the possession of data will be seen as a burden rather than an asset, a liability that requires constant, active mitigation instead of passive storage.
By 2030, we will look back at this era as the moment when the last vestiges of institutional secrecy evaporated, replaced by a world where every file is a potential leak and every server is a temporary waypoint for information that eventually wants to be free.
UGC Videos with AI Avatars — Realistic avatars for marketing






























