The Industrialization of Deception: Why Cybersecurity is Moving from Defense to Verification
The Economics of Automated Manipulation
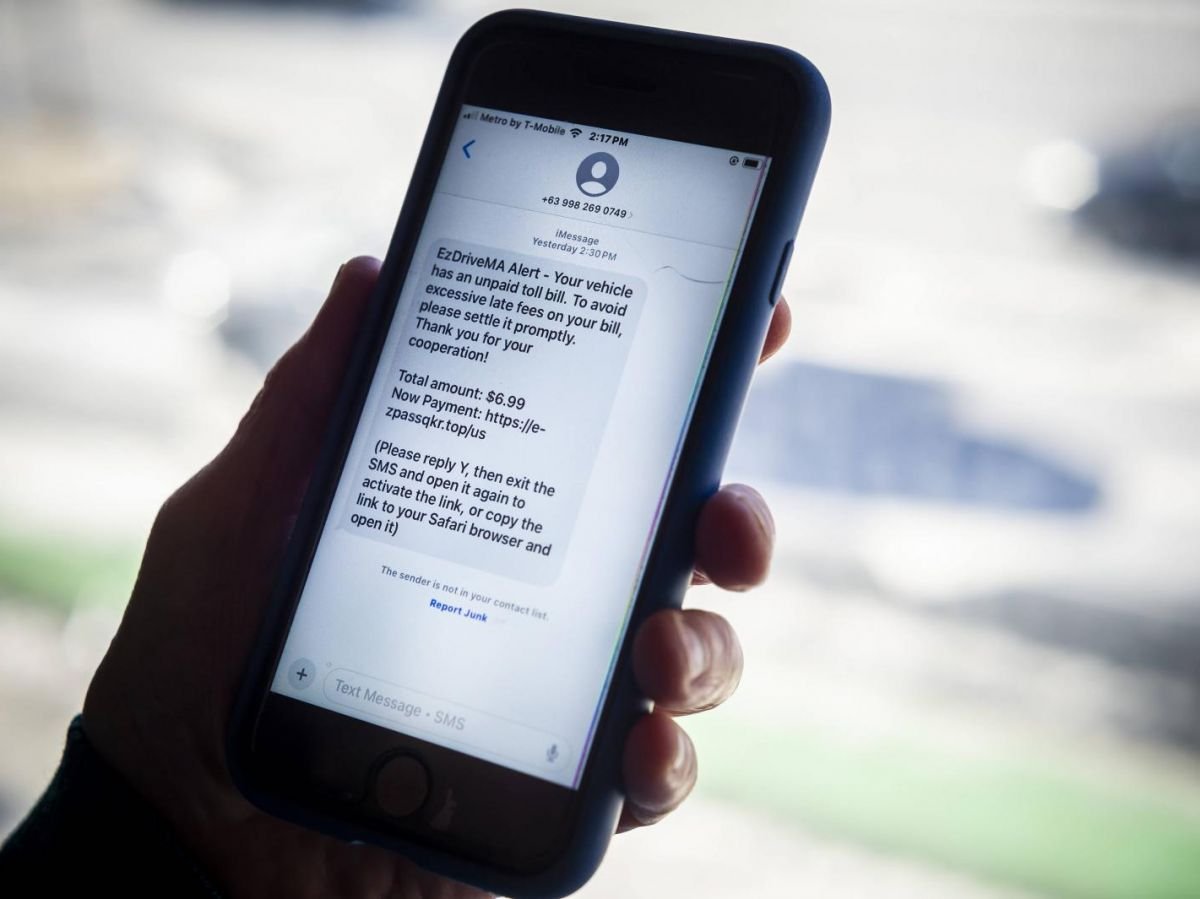
Cybersecurity is no longer a battle of individual hackers versus firewalls. We have entered the era of industrialized digital warfare. With over 348,000 recorded breaches in 2024 alone, the cost of executing a high-level manipulation campaign has dropped to near zero. This is a classic supply-side shock: when the tools to create fake identities and deceptive narratives become automated, the market is flooded with high-quality noise.
For years, enterprises focused on perimeter defense—keeping the bad guys out. That strategy is dead. In a world where identity is easily spoofed and social engineering is powered by large-scale data sets, the perimeter is everywhere. The real business threat isn't just a data leak; it is the systematic erosion of informational integrity that makes commerce possible.
The Verification Moat
As Baptiste Robert and other security researchers have pointed out, the ability to discern truth from manufactured fiction is becoming the ultimate competitive advantage. Companies that can verify the provenance of their data and the identity of their users will win. Those that rely on legacy trust models will be bled dry by automated fraud.
- Identity as a Service (IDaaS) will shift from a convenience feature to a core security requirement.
- Zero-Trust Architecture must evolve to include content verification, not just network access.
- Metadata Auditing will become a standard part of due diligence in M&A and vendor onboarding.
The business model of the internet has long relied on the assumption that a human is on the other side of the screen. That assumption is now a liability. We are seeing a liquidity crisis in trust, where the cost of verifying a transaction often exceeds the margin of the transaction itself.
Who Wins the War of Friction?
Low-friction GTM strategies were the darling of the last decade. But in an age of mass deception, friction is a feature. Requiring hardware-based keys or biometrics isn't just a security hurdle; it is a filter that protects the unit economics of a platform by pricing out automated attackers. Platforms that refuse to implement these hurdles will see their user bases diluted by bots, eventually leading to a death spiral of engagement and ad value.
"Cybersecurity is no longer about technology; it is about the psychology of trust in a digital environment where everything can be faked."
The winners in this new environment will be the verification layers. We are moving toward a bifurcated internet: a verified tier where business happens, and an unverified tier that is effectively a dark pool of automated noise. Investors should look for companies building the infrastructure for this verified tier. The value is no longer in the data itself, but in the proof of its origin.
I am betting against legacy social platforms that rely on unverified scale. The future belongs to closed, high-trust ecosystems with hard-coded verification. If you can't prove who your users are, your valuation is a work of fiction.
Faceless Video Creator — Viral shorts without showing your face






























