The Digital Basement: Where Virtual Code Meets Physical Crime
Lucas sat in a quiet cafe in Marseille, his thumb rhythmically scrolling through a stream of encrypted messages that felt less like a chat room and more like a marketplace for human vulnerability. He wasn't looking for software patches or leaked passwords to drain a bank account from a distance. Instead, he was scouting for an address, a security code, and the daily habits of a specific logistics manager whose life had been reduced to a set of coordinates by a stranger thousands of miles away.
For years, we viewed the digital and the physical as separate territories, distinct neighborhoods with their own rules and their own dangers. The hacker was a ghost in the machine, a flickering silhouette behind a screen, while the criminal was a body in the street. That wall has not just cracked; it has been dismantled, piece by piece, by the terrifyingly efficient architecture of modern messaging platforms.
The Architecture of the Shadow Market
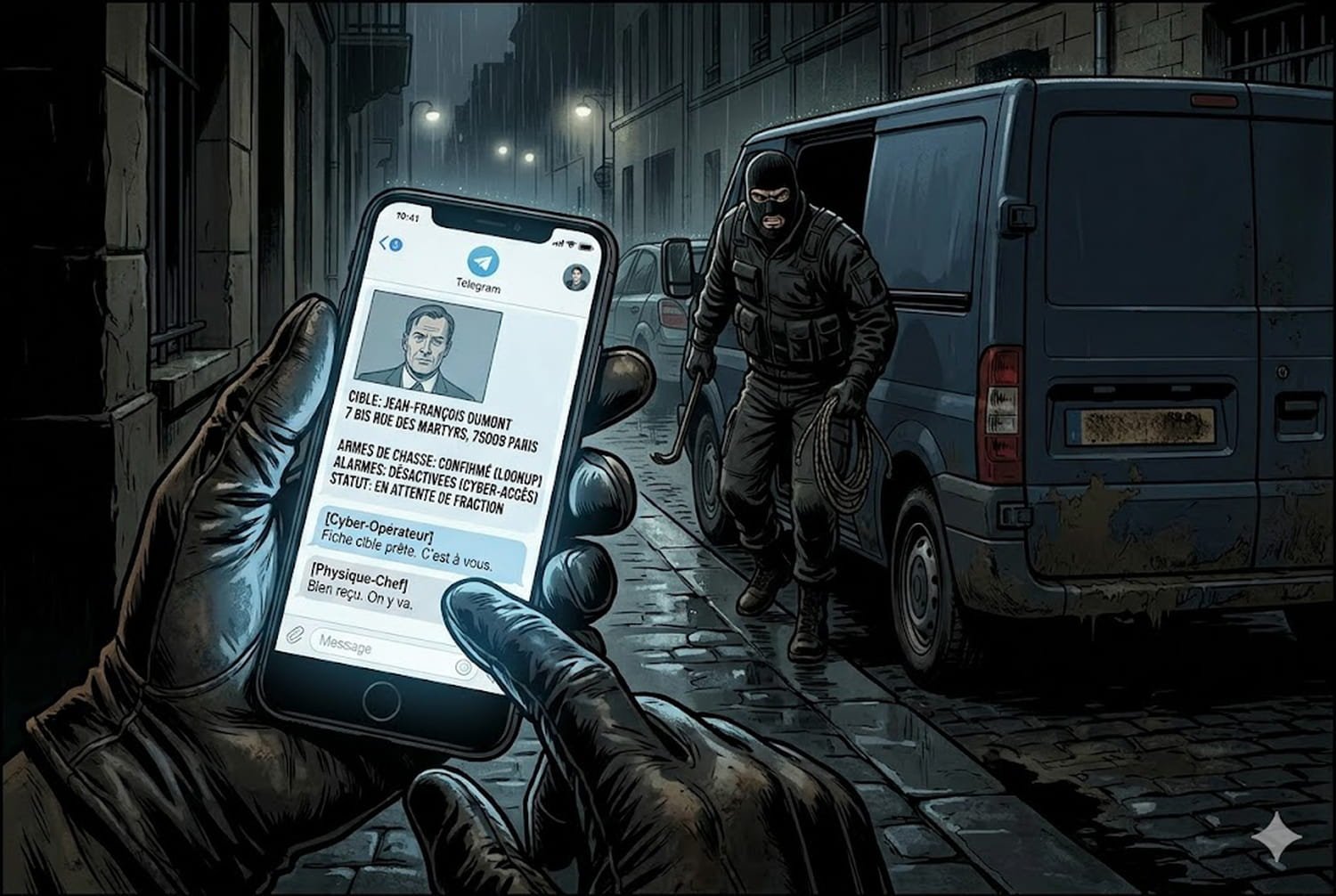
In the hidden corners of the internet, a new kind of commerce has taken root where data is no longer the end goal but the blueprint for a heist. We are seeing the rise of a hybrid class of threat where technical skill serves as the scout for physical violence. Visibility is the new currency, one digital forensic analyst told me, noting that information stolen in a corporate breach often ends up being sold to local gangs who prefer sledgehammers to scripts.
The ease of these interactions is what makes them so chilling. There is no longer a need for a complex network of informants or months of manual surveillance. A single vulnerability in a poorly secured database can yield the floor plans of an apartment complex or the private schedules of high-net-worth individuals, which are then auctioned off to the highest bidder in a matter of seconds.
The screen acts as a bridge, turning a data point into a target and a stranger into a victim with a clinical, terrifying speed that the law is struggling to match.
The geography of crime has shifted from the dark alley to the glowing screen. This proximity allows for a level of coordination that was previously impossible. A group in one hemisphere identifies a weakness, while a group in another carries out the manual labor of a break-in or an abduction.
A Fragile Social Fabric
As these two worlds merge, the sense of safety we once felt behind our locked doors begins to feel illusory. We have spent decades hardening our digital defenses, teaching people to use complex passwords and two-factor authentication, yet we are less prepared for the moment that digital negligence leads to a knock on the door. The human element, always the weakest link in security, is now being exploited in ways that are visceral and immediate.
It is a strange irony that the more connected we become, the more exposed we are to those who seek to use that connectivity against us. Is our intimacy with technology making us easier to track or easier to hurt? We provide the tools for our own surveillance every time we share a location or leave a digital footprint that we assume is private, forgetting that privacy is a luxury the internet rarely provides.
Behind every leak is a person whose sense of sanctuary is being traded like a commodity. The developer who accidentally leaves a database open isn't just risking a fine; they might be inadvertently handing someone the keys to a stranger's home. Responsibility is often diffused in these digital spaces, making it easy to forget that every byte of data represents a heartbeat.
Later that evening, the cafe in Marseille grew dark, the glow of phone screens lighting up faces like small, blue ghosts. Somewhere else, a door was being forced open because of a string of numbers typed into a chat window hours earlier. We are living in the static between the signal and the strike, waiting to see if our shadows will catch up with us.
AI PDF Chat — Ask questions to your documents






























